As the number of digital certificates increases, so do the number of PKIs (Public Key Infrastructures), making certificate management ever more complex. True “one-stop shops”, CLM (Certificate Lifecycle Management) solutions are becoming indispensable to monitor and manage the entire certificate lifecycle in a multi-PKI context.
Digital certificates and PKI, then and now
Certificates have long been limited in number and use, and confined to very specific cases. In addition, the distribution stage was reduced to a simple e-mail or publication in a directory, and deployment was limited to support for the SCEP protocol. In fact, these two stages did not even appear in the certificate lifecycle diagrams.
With the acceleration of the digital transformation, the need for digital certificate management has arisen. This role is fulfilled by the PKI (Public Key Infrastructure), whose objective is to provide a robust infrastructure for managing public keys and, by extension, the digital certificates that carry them.
In just a few years, the digitalization of many services has led to the mass use of certificates, particularly for machines (servers, IoT, mobiles, etc.). As a result, the volume of certificates to be managed has increased dramatically, while their lifecycle has been shortened and the number of PKIs has multiplied.
Towards a redefinition of the role of PKI
Today, companies manage a large number of certificates from a variety of sources. They are used to secure servers, applications, mobile devices, connected objects and more. The lifecycle of certificates has become more complex, requiring more rigorous management to ensure their validity, renewal and revocation. As a result, companies are finding it increasingly difficult to manage these certificates using traditional PKI.
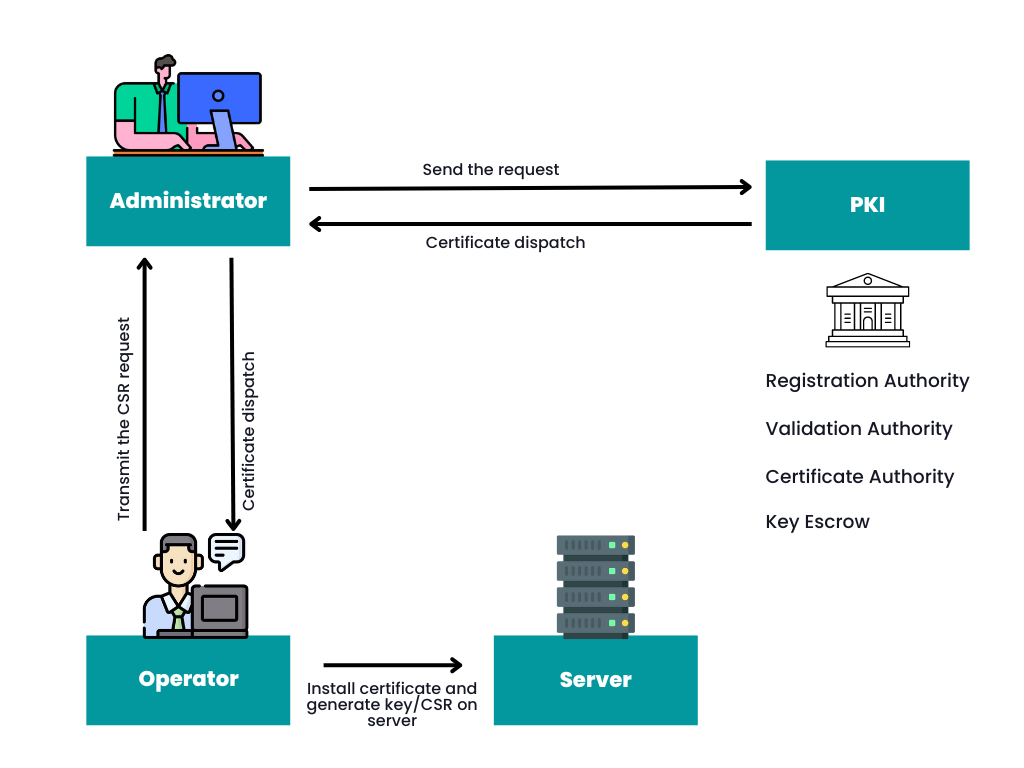
Until now, PKI has generally included:
- A certificate authority, for issuing certificates and authenticating the identity of correspondents;
- A validation authority, to check the validity of certificates and ensure that they are not revoked;
- A key escrow, for storing the encryption keys of issued user encryption certificates, in order to avoid any loss of data due to the loss of the encryption key;
- A registration authority, responsible for verifying and authenticating the identity of the certificate applicant.
But in a multi-PKI context (external or internal), this model no longer meets organizations’ needs for a more comprehensive approach to certificate management. New services have become indispensable, supported by CLM solutions: discovery and inventory of certificates in the various PKIs, real-time supervision of their validity and multi-channel notifications, distribution and deployment, and finally automation of certificate lifecycle management.
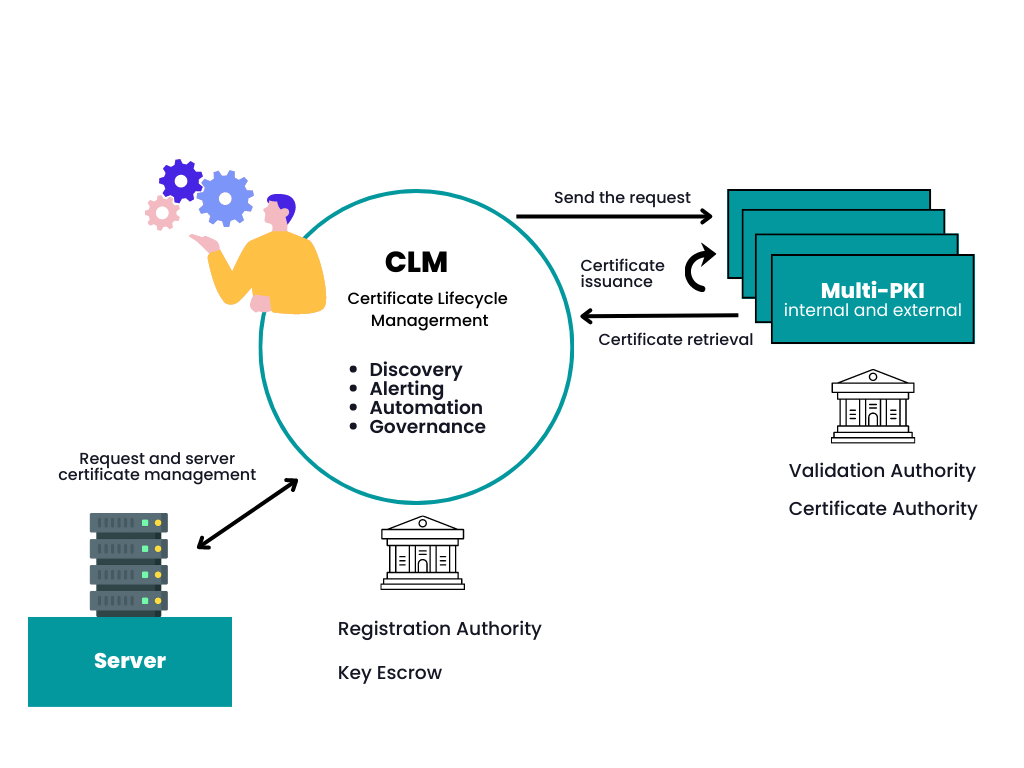
CLM: supervision of the entire PKI certificate lifecycle
CLM is never intended to replace PKI, but to complement it. A modern PKI must now comprise several certificate authorities, several validation authorities and a CLM solution. This combination enables efficient, secure management of the entire digital certificate lifecycle, combining digital trust, security, scalability and operability.
In a company, we typically find: a Windows certificate authority (to manage the Windows server installed base), a technical certificate authority (to manage all internal requests outside the Windows context), and one or more public certificate authorities (to protect publicly exposed services and sites).
By adding the four missing components to a PKI, a simplified, single registration authority and a key escrow, the implementation of a CLM solution provides the services expected of a modern certificate management system, in a certificate authority-agnostic way, to address all current use cases.
It is of course possible to use one or more PKIs without a CLM: one or more certificate authorities, each with its own validation authority, enable the company to produce certificates and validate their revocation, but without any ancillary services. However, the combined PKI + CLM approach offers a more robust infrastructure for public key management, certificate validation and all associated services, meeting today’s security and digital certificate management needs.
