Digital certificates are a key component of digital trust solutions. We are involved in the entire lifecycle of certificates, from their creation and use in electronic signature, strong authentication and legal archiving projects through to their automated renewal.
Creating digital certificates: PKI integration

Implementing a PKI is essential for generating digital certificates to be used for encrypted transactions and identification and authentication purposes.
We can help you to choose the PKI which best suits your needs from the main solutions on the market: OpenTrust, Microsoft ADCS, Nexus, RedHat and EJBCA Enterprise by Primekey, one of our partners. We can also help you to integrate it into your information system.
Using digital certificates: use cases

Electronic signature
Digital certificates enable you to sign documents to give them legal validity and guarantee their integrity and non-repudiation.

Authentification
They are easy to manage and use on a day-to-day basis and offer a high level of security to authenticate both users and servers.

Archiving
Using digital certificates enables you to implement long-term digital archiving with legal value.
Monitoring and automatically renewing digital certificates
Each certificate has a unique expiration date. Our BerryCert solution inventories, monitors and automates the renewal of the thousands of digital certificates in your organization to prevent service outages.
Certificate Lifecycle Management solution
BerryCert helps reduce your operating costs by automating time-consuming, zero-value-added certificate lifecycle management tasks.

Automatic renewal of certificates
BerryCert automatically renews each of your digital certificates before they expire.
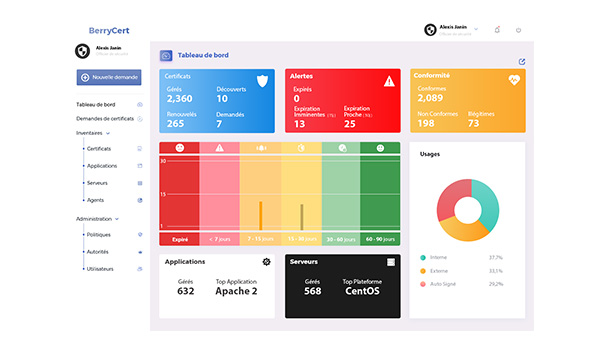
Monitoring console
This provides you with 360º visibility of your digital certificates (valid, nearing expiry or expired) and regular reports on completed renewals.
Want to learn more? Read our related articles
CIO: Plan ahead for digital certificate validity periods being cut to 90 days with an automation solution
Following the CA/B Forum meetings held in March 2023, in its “Moving Forward, Together” roadmap Google announced plans to reduce the maximum validity of SSL/TLS certificates on Chrome to...
PKI + CLM: the essential duo for managing digital certificates
As the number of digital certificates increases, so do the number of PKIs (Public Key Infrastructures), making certificate management ever more complex. True “one-stop shops”, CLM...
Tightening security for your applications: how to audit your digital certificates, and why
When it comes to building channels you can trust between an organization’s various networks and nodes, nothing beats electronic certificates. Misconfigured and non-compliant certificates can leave...