

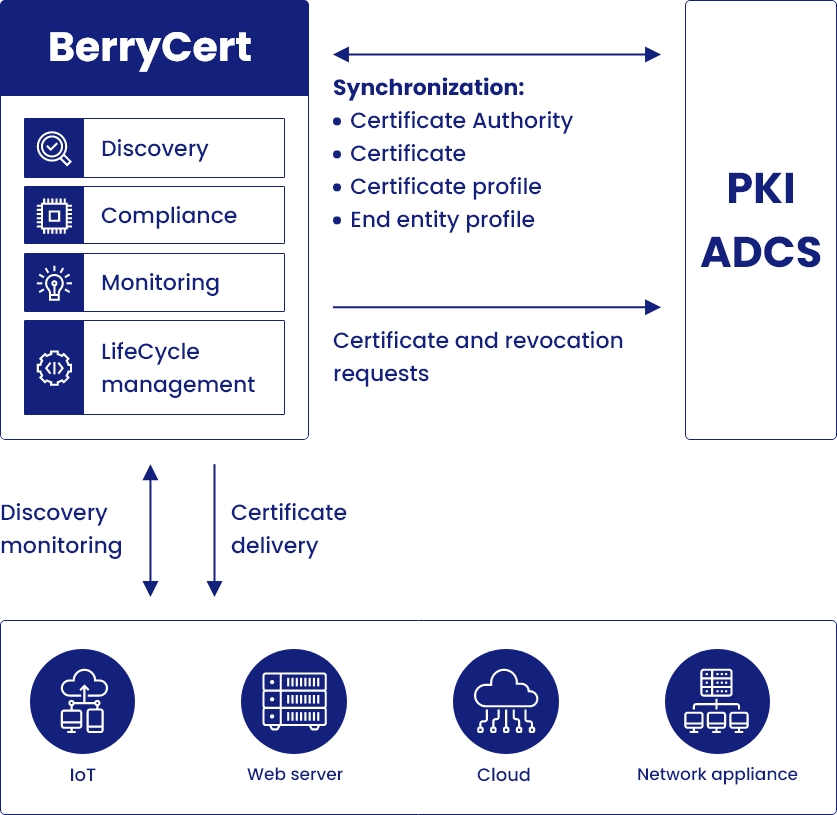
The Microsoft ADCS PKI is designed for use by Windows services, not for external requests, or any other types of requests for that matter. Here we look at how to extend the efficiency and agility of your Microsoft ADCS PKI with BerryCert, an intelligent certificate management engine.
With its Active Directory Certificate Services (ADCS) component, Microsoft provides a Public Key Infrastructure (PKI) solution that is fully integrated into the Windows ecosystem.
Renew the user experience
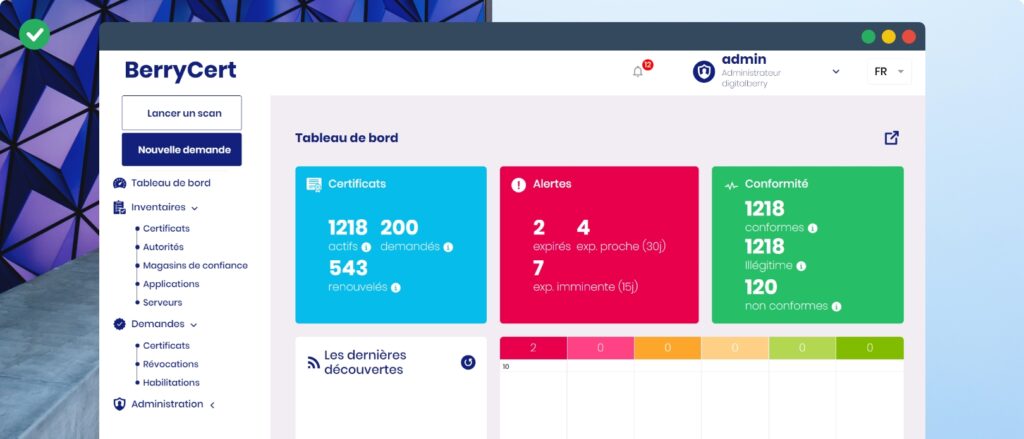
User interface and supervision
Your Microsoft ADCS PKI provides an interface that is compatible only with Internet Explorer, and only up to version 11. What’s more, its features are limited and it is not particularly user-friendly.
- The BerryCert solution provides an intuitive GUI focused on user experience: dashboards for monitoring, sort and select functions, exports, and audit reports.
- Through role management, you can provide interfaces contextualized to each user, configure uses, and facilitate the digital certificate requests and revocations of your Microsoft ADCS PKI.
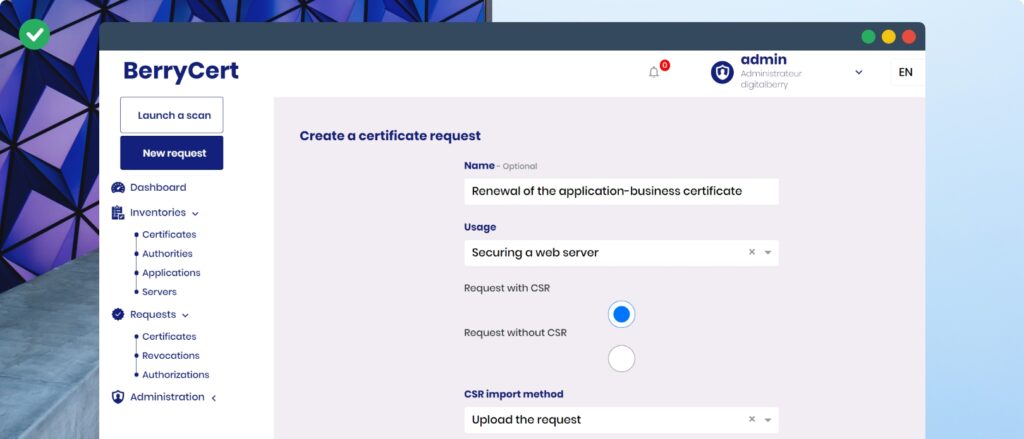
Certificate requests simplified by issuance policies
The process for requesting new certificates using Microsoft tools is complex. The user has to choose the certificate template and key size via tools that are far from straightforward.
- BerryCert offsets this complexity by providing users with business options so that they can make informed choices by themselves. These choices are configured via issuance policies that establish the link between the PKI (CA, certificate template) and a BerryCert compliance policy.
Develop uses
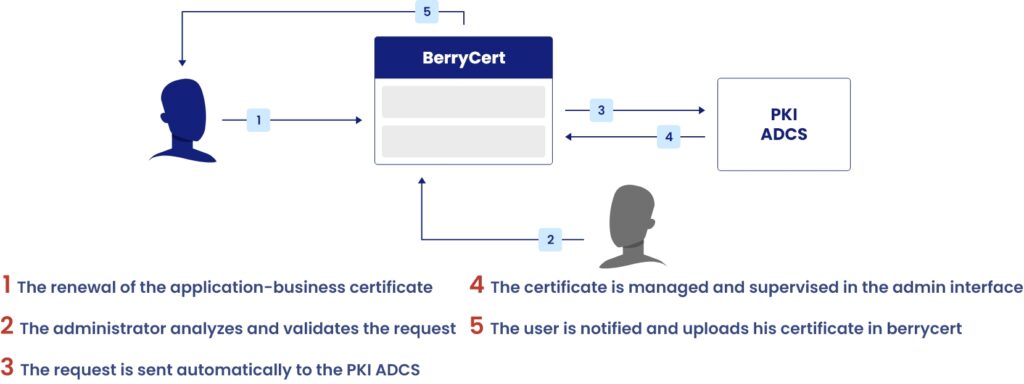
Remote Registration Authority (RA)
Are you looking to set up certificate request approval workflows? While you can configure approvals in a Microsoft ADCS PKI, this requires access to the server hosting the CA (certificate authority), since the approval is carried out on a local interface.
You are advised to limit the exposure of your CA to as few persons as possible, and yet the RA and CA functions get mixed up in the Microsoft ADCS PKI. You must grant access to the PKI server to manage request approvals, which is not advised.
- With BerryCert, administrators can configure user paths by managing approval rights independently of the CA server. The solution is positioned as a remote RA of the Microsoft PKI to manage the validation of requester identities.
Roles and organization
- BerryCert lets you define user profiles by assigning them individual rights on resources. This serves to follow the principle of least privilege.
This definition of the role is consistent with the standards in force: eIDAS, RGS and CC. - Functional perimeters can be configured to compartmentalize each user group’s business data, which can’t be done using the Microsoft ADCS PKI alone. Depending on the rights and authorizations, each user can thus request a certificate based on a predefined issuance policy.
Set up bespoke approval workflows
- With its workflow engine, BerryCert offers a customizable interface allowing organizations to configure the processes used to manage their digital certificates.
- BerryCert offers wider customization possibilities on the approvals (e.g. management of organizations, notifications, grouped approvals).
Strengthen usability
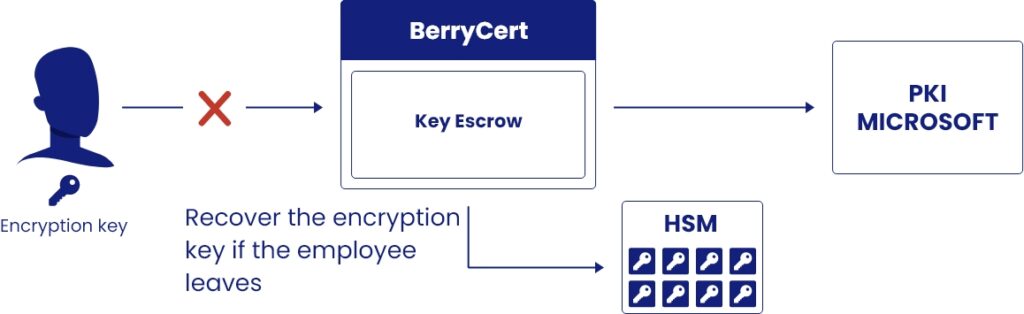
Key escrow authority
In the Microsoft ADCS PKI, the key escrow system is difficult to maintain sustainably without risk. In fact, clients run the risk of losing escrowed keys in the event of the departure of the recovery agent, as the escrow system uses cryptographic resources associated with users rather than centralized cryptographic resources to encrypt and recover keys.
- Conversely, BerryCert offers centralized key encryption management, and associates its management with a role. The result is easier key administration. The solution allows you to use an encryption key centralized in a Hardware Security Module (HSM) guaranteeing a higher level of security.

Configuration of administrator notifications
Inside your Microsoft ADCS PKI, the notification possibilities are fairly limited, with just one channel via e-mail, and fixed recipients (often a shared inbox), to say nothing of the scant possibilities for customizing the the e-mail in question.
- With BerryCert, the notifications proposed are multi-channel: email, internal notification, ticketing tools, etc.
Through notification management, you can define your recipients, the sending frequency.
You can thus make sure you pass on the right information concerning certificate statuses to those concerned, without overloading their inboxes with needless communications.
Centralize and automate the configuration of the CAs
In the Microsoft ADCS PKI, a Certificate Authority equates to a configuration on a given server. If managing multiple CAs, you thus need to replicate the same configurations on the other servers. This means a risk of inconsistency between the configurations of each server, which ultimately renders their management more complex.
- Using BerryCert, you can manage several Microsoft CAs by simply applying the same configurations.
In addition to the Microsoft CA, BerryCert can manage your other PKI via a single interface. Consequently, users can simplify their certificate requests via business uses.
Reconcile your security teams with your operating teams
Using your Microsoft ADCS PKI, you can control who makes certificate requests. However, you will be unable to subsequently check that a certificate has only been deployed on a single application, and so reduce security risks in case of the key’s compromise.
- With its system for continuously monitoring the certificates deployed in your applications, BerryCert allows your security teams to detect multiple installations of a certificate and thus raise alerts to the operating teams.
Conclusion
- The Microsoft ADCS PKI was designed for Windows services, not for external requests, or any other types of requests.
- You can unleash the performance, security and usability of your Microsoft ADCS PKI thanks to a workflow engine.
- This provides a perfect response to your PKI’s limitations by centralizing and automating the management of your certificates.
- In addition, using a single solution, you can manage your other PKIs, or perform your PKI migration operations.
