
Generating self-signed certificates is often used as an alternative, as they are less expensive and easier to produce. Because of this, some application operators opt to go down this route rather than use certificates signed by a trusted third-party Certificate Authority — a much more time-consuming and highly regulated process.
However, to protect your company’s brand image and security, we do not recommend working with self-signed certificates. In this article, we’ll take a closer look at the risks inherent to doing so.

What is a self-signed certificate?
A self-signed certificate is a certificate that is not issued by a known, respected certificate authority. In other words, it can’t be trusted. It’s as if you were to issue your own ID. Because you’re the only person who recognizes it, the card has no inherent value.
How can you tell if a certificate is self-signed?
A quick way of telling whether a certificate is self-signed is to simply check whether the issuer and subject are identical. Be warned, though: in some situations, you’ll need to go further in your research. If you want to be extra-sure, you’ll need to check whether or not the certificate is self-certified. In technical terms, this means that the digital signature has been issued by a private key linked to a public key within the certificate. Tools such as OpenSSL are needed to run these checks.
What are self-signed certificates used for?
They’re often used in temporary, testing and pre-prod environments, for internal needs and for installing and assessing tools and applications.
Standard IS processes are often long-winded, and because engineers generally need instant solutions, they sometimes choose to work with self-signed certificates.
What are the risks of using self-signed certificates?
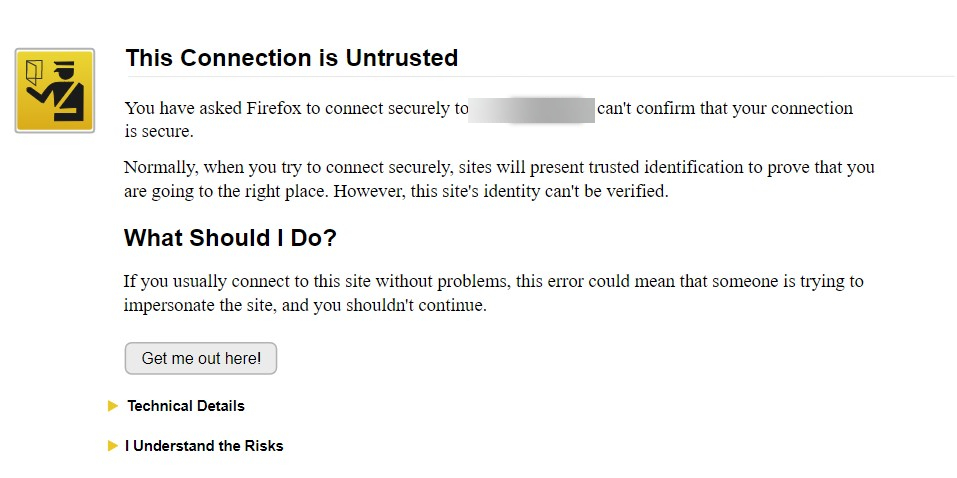
When you use a self-signed certificate on a public website, all browsers display a security notification that can prompt users to leave the page, as they worry their personal data isn’t safe. Using them impacts on users’ trust and confidence, which causes your brand image to plummet and your sales to drop.
The risk of using a self-signed certificate on an internal website is often minimized because the websites are generally harmless. Staff get into the habit of ignoring security notifications, making them vulnerable to malicious websites and other threats. If the same security alert pops up for a third-party app, they will log in and jeopardize your information system. This is why it’s crucial you raise team awareness of the issue.
Another major risk that should be taken into account is that self-signed certificates cannot be revoked. This is dangerous from the company’s perspective, should said certificate’s private key be compromised.
What’s the best way of mitigating this risk?
Preventing security alerts from popping up on your website and applications is easy: use certificates signed by a trusted authority. For public websites, this authority should be recognized by default across various browsers. For internal applications and websites, it should be recognized by staff browsers.
A CLM tool like BerryCert lets you manage an up-to-date inventory of your active certificates and map and detect self-signed certificates within your IS. It also lets you issue certificates quickly to your IT and production teams, all while guaranteeing compliance and traceability.
